Want to contribute to this article?
The core of data security in a post-GDPR world is privacy by design.
Privacy can no longer be bolted on as an afterthought.
You must be able to demonstrate to an ISO 27001 auditor or the Information Commissioner's Office that your information streams are built around private, secure data management from the start.
Electronic quality management systems, such as EQMS by Qualsys, are an ideal way to achieve this.
Here's how.
The privacy by design checklist
Kate Armitage, Head of Quality Assurance at Qualsys, put together a privacy by design checklist to help businesses prepare for the GDPR in early 2018.
The checklist lists the core tenets of privacy by design.
An infrastructure overhaul, like implementing a new governance, risk and compliance software system, is the ideal opportunity to bake privacy by design into your business operation.
Here's how EQMS by Qualsys fulfils 5 core components of privacy by design.
1. Embedded privacy
EQMS as a system has data privacy at its core.
The system is hosted at a secure ISO 27001-certified data centre or on customer premises.
Data housed within EQMS is password-protected, pseudonymised and encrypted, including encrypted data backups and transport encryption via HTTPS into the system itself.
And EQMS developer Qualsys commits to data governance with documented information security, GDPR, security incident and business continuity policies.
Access our information security credentials

2. Privacy as default
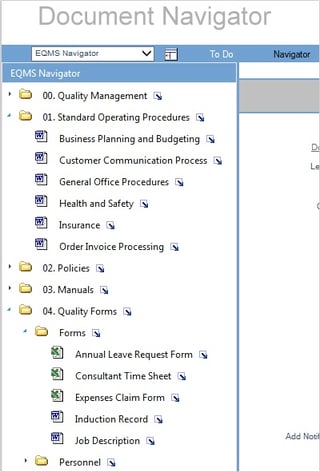
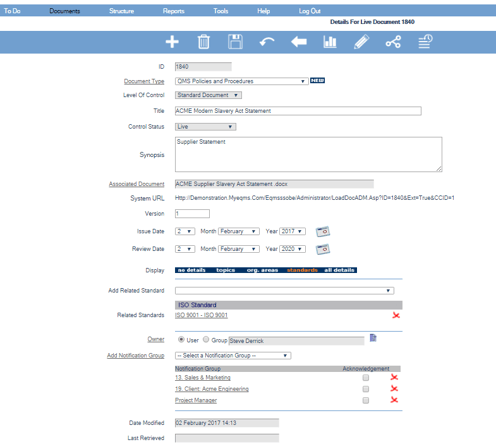
The Document Manager module is designed to store business documentation electronically, securely and privately by default.
Users access the system with a unique log-in.
Administrators set access rights for particular users and groups, allowing only approved, read-only documentation to be visible.
While audit trails, electronic signatures and version histories allow complete traceability of each document.
Archived and superseded documents cannot be tampered with or deleted, providing an incorruptible data trail.
The module keeps a complete record of all reviewing and approving activity, storing responses, names, dates and other compliance-related information against target deadlines for an integrated and audit-friendly data repository.
Access Document Manager datasheet
3. Visibility and transparency
Privacy by design demands transparent data processing and clear 'cards on the table' with regards to how personal data is stored and used by businesses.
Document Manager administrators can view the entire architecture of their business data from a single source, allowing good data governance to be enforced and audited quickly and easily from the top down.
And properly organising and securing electronic data with Document Manager simplifies response to subject access requests, including the 30-day turnaround time enforced by the GDPR.
4. Proactive not reactive
How will your business react in the event of a data breach?
Or if severe weather knocks out your data centre?
Or if a process change impacts your data processing?
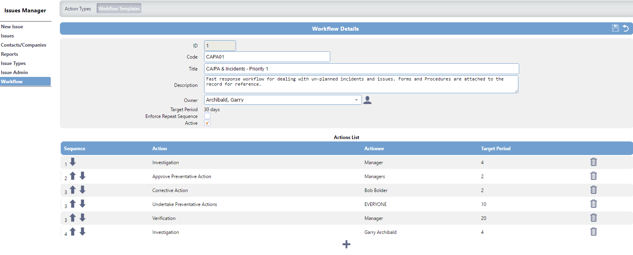
Building pre-prepared action workflows within Issue Manager allows businesses to take a proactive approach to data privacy and anticipate privacy-invasive events.
Construct a workflow. Assign appropriate personnel. Build the necessary steps and actions, then set response times for a controlled, standardised, specified approach to potential privacy disruption events.
Access Issue Manager datasheet
5. Simplicity
Privacy by design doesn't mean complex and multi-layered data mazes which are impossible to penetrate.
It should seek to accommodate all legitimate data interests and objectives in a positive-sum and simple 'win-win' manner, rather than through a dated, zero-sum approach where unnecessary trade-offs are made.
Data should be protected within an easy-to-navigate and user-friendly space for full control and visibility - duplicated, obfuscated or lost data is insecure data.
Document Manager's customisable document structure and privacy-default settings allows users to access, trace and track information streams without undue complexity or duplication of effort, cementing privacy as new data is added into the system.
Next steps
Learn more about electronic privacy by design and request GRC software pricing information here:






Share your thoughts on this article